Don’t Get Hooked: A Guide to Recognizing and Avoiding Phishing

Don’t Get Hooked: A Guide to Recognizing and Avoiding Phishing
As financial professionals, we understand how vital it is to safeguard your personal and financial information. Unfortunately, in our increasingly digital world, cybersecurity risks, such as phishing attacks, have become a prevalent issue that can compromise your financial health and personal identity.
Phishing is a deceptive practice employed by hackers to trick you into divulging sensitive personal or account data, often via email or texting. As cybercriminals refine their tactics, distinguishing between phishing and legitimate communication is becoming more challenging. However, the good news is that there are strategies you can adopt to help defend yourself from these attacks by recognizing the most common tactics.
In this blog, I’ll provide a comprehensive overview to help you spot a fraudulent email or text message.
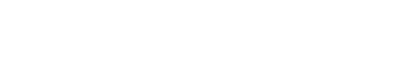
Seven Signs of a Phishing Email
SecurityMetrics.com, 2023
1) Most Companies and Government Entities Won’t Ask for Personal Information Through an Email
If you receive an email asking for sensitive information and are unsure if it’s legitimate, the best approach is to call the company directly to ask if the request is authentic. For example, DO NOT CLICK if the email appears to be from a credit card company saying your card is frozen due to unusual activity and asking you to click a link to reactivate it or provide your password. Instead, call the number on the back of your card to verify the request. Chances are, if it asks for your personal information, it’s a phishing attempt.
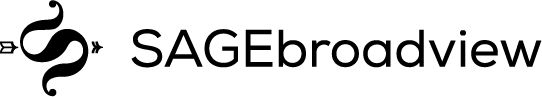
The IRS Will Never Email Demanding Immediate Payment
UTRGV.edu,The University of Texas Rio Grande Valley, 2023
2) Look Out for Generic Greetings
This is a great way to identify potential phishing emails! Phishing emails typically use generic salutations, such as “Dear Valued Member,” “Dear Account Holder,” “Dear Customer,” or, as in the example below, “Dear User.” Most companies you work with know your name. They will address you by name, especially if they need you to respond to a request for information or ask you to click on a link. If you receive an email requesting an action without a personalized salutation, be alert!
Generic Greetings Are a Clue
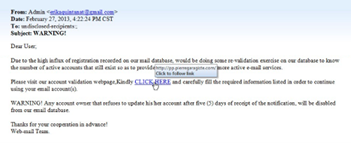
TN.gov, 2023
3) Be On The Lookout for Fake Email Addresses
The best ways to check for phishing are to take your time to closely examine the sender’s email and to look for spelling errors and incorrect domain names.
Let’s take a look at a few examples:
- The company name looks correct, but the email address uses a slightly different domain.
- An email from: Amazon ([email protected])asks you to update your account information. If you look closely, although the first Amazon is spelled correctly, the email address is missing the “a”.) This is a common approach.
- Another is using the company name before the @ sign, like Facebook ([email protected]). Your eye sees Facebook in the email address, but this domain is @info, not @Facebook. Red flag!
Spotlight on Fake Email Address

CheapSSLSecurity.com, 2023
- The email domain is spelled incorrectly.
- An email from“[email protected]” prompts you to click a link to resolve a recent issue. This is tricky; the ‘L’ in PayPal is a capital ‘i’!
- They add “-”s (dashes) to break up the name of the company in the email domain:
- Your bank is MyBank. You receive an email from “[email protected]”requesting personal data. Looking closer, the correct domain for your bank is @mybank.com with no “-”. Not to mention, it is unlikely that you’d receive an email from the CEO of the bank. If it seems off, it likely is.
- An email from “[email protected]”reports unauthorized access to your Microsoft account. Microsoft’s real domain is “microsoft.com”, not “micro-soft.com”. Be on the lookout for email domains (the word before the @) with “-” dashes, numbers, or extra dots “.”s.
4) Notice spelling and grammar errors
Many phishing attempts include grammatical and spelling errors. This is a big red flag, of course. When reading emails requesting information or asking you to click on a link, take your time. If you notice spelling or grammatical errors in the email, you can be confident that they are fraudulent.
Watch Spelling & Grammar

GulfShoreInsurance.com, 2023
5) Hover Over Any Hyperlinks within the Email
Take the time to hover over links within an email. Before clicking on anything that is hyperlinked (is underlined and will take you to a web page), move your mouse over the link to see the URL. Do you recognize a legitimate company website? Pay attention to spelling errors in the company’s name, dashes, periods, and numbers.
- A common phishing tactic is adding an extra letter ‘S’ or ‘A’ in the spelling of the company name within the URL—for example, walmarts.com or www.costcoo.com.
- The ‘O’ (letter O) has been replaced with ‘0’ (zero)—for example, yah00.com.
Check Out the Hyperlinks
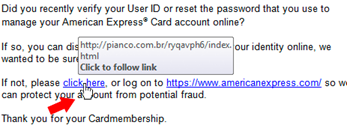
Law.UPenn.edu, 2023
6) Legitimate Emails From Companies Do Not Include Unsolicited Attachments
Unsolicited emails that contain attachments reek of hackers. Typically, authentic institutions don’t randomly send you emails with attachments, but instead direct you to download documents or files on their website. Look for high-risk attachment file types, including .exe, .scr, and .zip. (When in doubt, contact the company using contact information from their website.)
Watch Out for Unsolicited Attachments
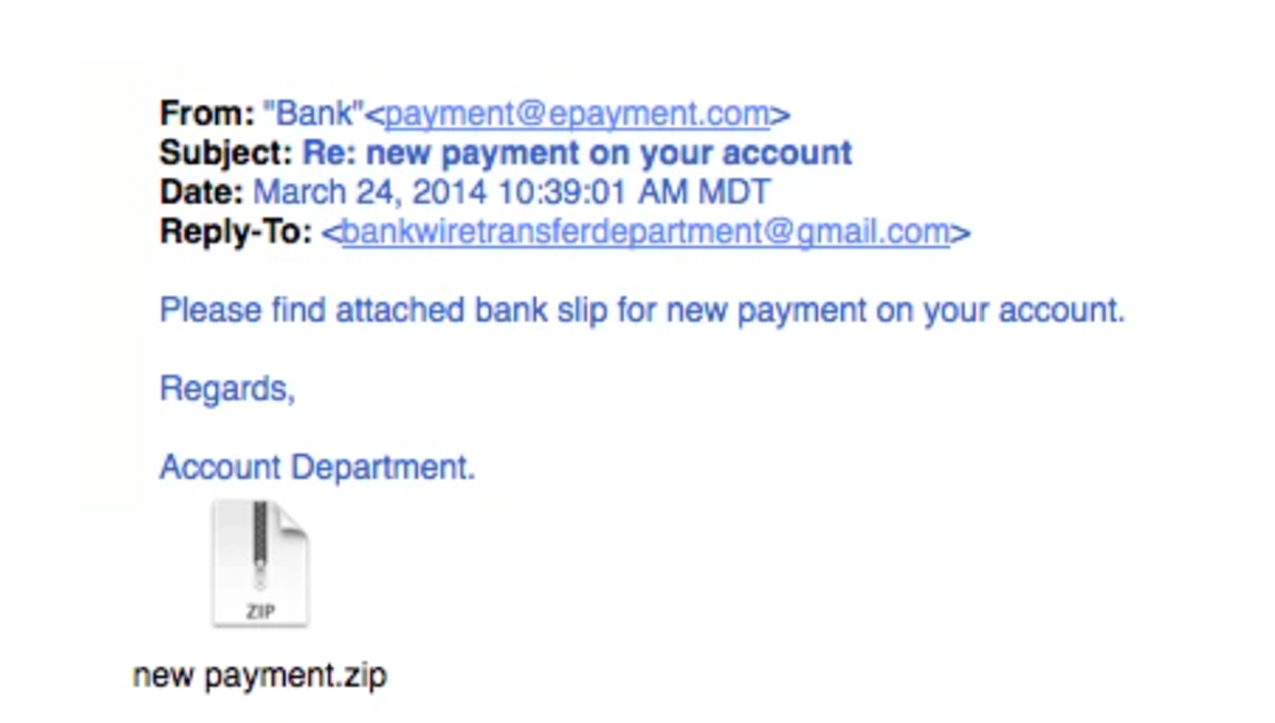
SecurityMetrics.com, 2023
7) Legit Company Links Match Legitimate URLs
Just because a link says it will send you to one place doesn’t mean it will. Double check URLs. If a hyperlink’s URL doesn’t seem correct or doesn’t match the context of the email, don’t trust it. Always hover your mouse over embedded links (without clicking!) and ensure the link begins with https://.
- You may hover over a hyperlink that says, “www.outlook.com,” but when mousing over it, you see “www.outl0ok-login.com.” The “o” in “Outlook” has been replaced with a zero “0.” Don’t click!
- You may hover over a hyperlink that says “www.netflix.com,” but when you mouse over it, you see “www.netflix-verify.com.” If you type “www.netflix-verify.com” into your search bar, you’ll realize that this is not a real site. In addition, note that it does not start with https://.
Let’s take a quick quiz:
Which of the following is phishing vs. a legitimate URL?
Paypal Example:
1. https://www.paypal.com/za/webapps/merchant
2. https://www.196.14.342.paypal.com/us
3. https://www.paypal.com/signin?country
4. https://www.paypal.com/za/webapps/mpp/personal
Which of the following is phishing vs. a legitimate URL?
Amazon Example:
1. https://www.ammazon.com/homepage.html
2. https://www.amazone.com/
3. https://www.amazon.com
4. https://www.amazon.us-com/webapps
(Answers at the end of the Blog)
Additional Red Flags
Attackers employ specific strategies in both emails and texts to deceive victims. These strategies often leverage fear, urgency, authority, curiosity, and trust. By understanding these, you can better recognize potential threats.
Urgency
Attackers may create a sense of urgency, compelling victims to act without thinking.
Examples:
- Email Example: “Suspicious activity detected! Click this link within the next 30 minutes to avoid account suspension.”
- Text Example: “ALERT: Unusual activity detected on your credit card. If you don’t respond within 30 minutes, your card will be blocked. Call this number to verify transactions: (123) 456-7890.”
Remember: Always question why immediate action is required. Banks typically recommend calling the number on the back of your credit card for any issues, not a non-official number.
Authority
Phishers may impersonate authority figures to manipulate victims into complying.
Examples:
- Email Example: “I need you to send me the company’s credit card details ASAP. I have a critical business expense that can’t wait.”
- Text Example: “This is the IRS. Our records show that you have an outstanding tax debt. To avoid penalties, pay your debt now by clicking this link: irspayments.com.”
Remember: Always verify out-of-the-ordinary requests from authority figures. Government entities don’t typically initiate contact via text.
Fear, Curiosity/Intrigue, and Trust
Other tactics include instilling fear, provoking curiosity or intrigue, and abusing trust.
Examples:
- Email Example: “You have unpaid taxes! If you don’t resolve this issue within 24 hours, legal action will be taken.”
- Text Example: “Hey, it’s Mike from work. I’m locked out of my email. Can you send me a password? I need to access a file urgently.”
Remember: Be skeptical of threats, unexpected rewards, and unusual requests for sensitive information. Always verify these kinds of messages independently.
Final Tips to Protect Yourself
In today’s increasingly digital world, phishers are advancing their techniques, including employing AI tools like ChatGPT to craft convincing messages. Here are some final tips to protect yourself:
1. Be cautious of unexpected messages, even from trusted sources (such as Google, Microsoft, your bank, your employer, etc.).
2. Always check the sender’s email address to ensure it’s genuine.
3. Hover over links to see where they lead before clicking. If it seems suspicious, do not click.
4. Be aware that phishing can occur via text messages, too. Do not act on a text unless you know the sender.
5. When in doubt, do not reply to the message. Instead, contact the sender through a known, secure method (like a phone call or email to a contact in your address book or a number from a billing statement) to verify the message’s legitimacy.
In wrapping up, the most effective safeguard against phishing attacks is a blend of vigilance and healthy skepticism. I encourage you to thoroughly scrutinize suspicious communication before clicking links, providing personal or financial information, or downloading attachments. As a financial professional, I work to grow and protect clients’ privacy and equip them with the necessary knowledge to ensure that they stay safe in this digital age. Securing your digital world is as crucial as securing your financial future.
Answers to the Quiz
PayPal example: B is a phishing link, the rest are authentic
Amazon example: C is an authentic link, the rest are phishing attempts
 Secure Document Sharing
Secure Document Sharing